wow-mcp
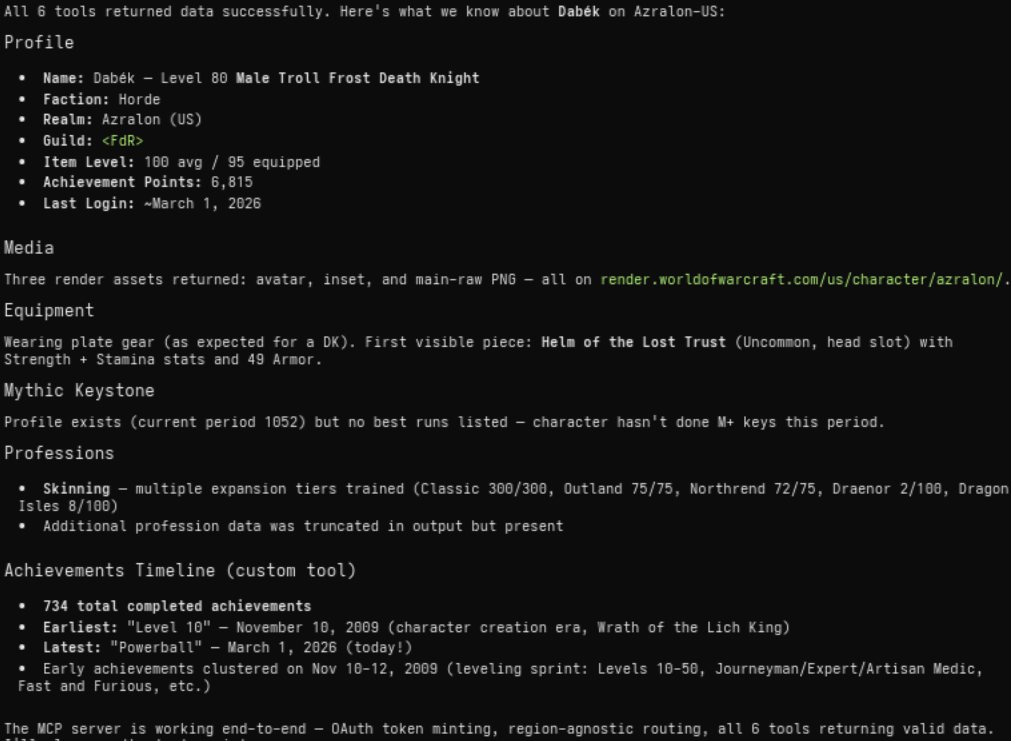
Provides comprehensive access to the World of Warcraft retail API, including both Game Data and Profile APIs, allowing users to retrieve detailed information on characters, achievements, auctions, mounts, professions, and PvP statistics across multiple regions.
Click on "Install Server".
Wait a few minutes for the server to deploy. Once ready, it will show a "Started" state.
In the chat, type
@followed by the MCP server name and your instructions, e.g., "@wow-mcpshow me the gear and stats for character 'Gingi' on Echo-EU"
That's it! The server will respond to your query, and you can continue using it as needed.
Here is a step-by-step guide with screenshots.
wow-mcp
MCP server that wraps the complete World of Warcraft retail API (Game Data + Profile) as 197 MCP tools. Supports OAuth 2.1 authentication (authorization code + PKCE for ChatGPT, client credentials for CLI tools) and is fully region-agnostic — every tool accepts region and locale as optional parameters, so a single server instance can query any region.
Quick start
cp .env.example .env
# Fill in BNET_CLIENT_ID and BNET_CLIENT_SECRET
npm install
npm run build
npm start # stdio transportDevelopment
npm run dev # runs via tsx (no build step)
npm run inspect # opens MCP Inspector UI
npm run lint # type-check only
npm test # run auth integration testsAPI coverage
All 196 retail WoW endpoints are registered as individual MCP tools, plus one custom computed tool:
Game Data API — 161 tools covering achievements, auctions, azerite essences, connected realms, covenants, creatures, guild crests, heirlooms, items, journals, media, modified crafting, mounts, mythic keystones, mythic raid leaderboards, pets, playable classes, playable races, playable specializations, power types, professions, PvP seasons, PvP tiers, quests, realms, regions, reputations, search endpoints, spells, talents, tech talents, titles, toys, and WoW tokens.
Profile API — 35 tools for character profiles, achievements, appearance, collections, dungeons, encounters, equipment, hunter pets, media, mythic keystone profile, professions, PvP, quests, reputations, soulbinds, specializations, statistics, titles, and guild endpoints.
Custom —
wow_character_achievementsTimelinebuilds a chronologically sorted timeline of completed achievements (computed, not a raw Blizzard endpoint).
Region & locale
Every tool accepts two optional parameters:
region—"us"(default),"eu","kr", or"tw"locale—"en_US"(default), or any locale supported by the target region (e.g."es_MX","de_DE","fr_FR","ko_KR")
No region configuration is needed in the environment. The same Battle.net credentials work across all regions.
Environment variables
See .env.example. Only two are required:
BNET_CLIENT_ID— Battle.net OAuth client IDBNET_CLIENT_SECRET— Battle.net OAuth client secret
Optional auth (OAuth 2.1 for the MCP HTTP endpoint):
MCP_AUTH_SECRET— passphrase that enables OAuth. Used as the login on the/authorizepage (for ChatGPT / browser clients), as theclient_secretforclient_credentialsgrants, and directly as a staticBearertoken for simple clients (Warp, curl, etc.).MCP_TOKEN_TTL_SECONDS— access token lifetime (default:3600)DATABASE_URL— PostgreSQL connection string (e.g.postgresql://user:pass@host:5432/db). When set, OAuth tokens, clients, and auth codes are persisted in PostgreSQL so they survive restarts. When absent, in-memory stores are used. Thedocker-compose.ymlsets this up automatically.
When MCP_AUTH_SECRET is set, the server exposes a full OAuth 2.1 provider:
GET /.well-known/oauth-protected-resource— RFC 9728 metadataGET /.well-known/oauth-authorization-server— RFC 8414 metadata (includescode_challenge_methods_supported: ["S256"])POST /register— RFC 7591 dynamic client registrationGET|POST /authorize— authorization code + PKCE flow with passphrase loginPOST /token— supportsauthorization_code(with PKCE) andclient_credentialsgrants
The MCP_AUTH_SECRET value can also be passed directly as a Bearer token (e.g. Authorization: Bearer <your-secret>) — useful for clients like Warp that don't support OAuth flows.
If MCP_AUTH_SECRET is not set, the server runs without auth.
Optional tuning:
LOG_LEVEL— pino log level (default:info)HTTP_TIMEOUT_MS— request timeout (default:15000)HTTP_RETRY_LIMIT— retry count (default:2)CACHE_TTL_SECONDS— response cache TTL (default:300)CACHE_SIZE— max cached entries (default:500)
Testing
npm testIntegration tests use Node's built-in test runner (node:test) via tsx — no extra test dependencies. The suite spins up the server on a random port with test credentials and verifies OAuth 2.1 auth end-to-end:
Serves
/.well-known/oauth-protected-resourcemetadataServes
/.well-known/oauth-authorization-servermetadata with S256Registers a new client via
POST /registerRejects
/mcpwithout a token (401 withresource_metadatahint)Rejects
client_credentialswith wrong secret (401)Issues token via
client_credentialswith correct secret (200)Completes full authorization_code + PKCE flow (register → authorize → token → /mcp)
Allows
/mcpwithMCP_AUTH_SECRETas a static bearer token (200)Rejects
/mcpwith a bogus token (401)
Docker
docker compose build
docker compose up -dSecrets are injected via .env on the host (not committed). The container runs as a non-root user with production dependencies only.
The compose stack includes a PostgreSQL instance for persistent OAuth token storage. PostgreSQL data is bind-mounted to ./data/postgres/ on the host (maps to /var/lib/postgresql/data inside the container), so it persists across container recreates, host reboots, and Docker engine upgrades. DATABASE_URL is pre-configured automatically.
NAS / self-hosting note: make sure the
data/postgres/directory is on a reliable filesystem. Back up this folder to preserve all OAuth state.
Architecture
src/
index.ts # entry point — loads env, starts server
app.ts # HTTP server factory (all routes)
auth.ts # OAuth 2.1 provider (metadata, registration, authorize, token, bearer validation)
config/
env.ts # zod env parsing (credentials + tuning)
regions.ts # region enum, API hosts, OAuth URL
store/
types.ts # OAuthStore interface + record types
memory.ts # in-memory store (default)
postgres.ts # PostgreSQL store (when DATABASE_URL set)
index.ts # factory — picks store based on env
mcp/
tools.ts # auto-registers all endpoints + custom tools
schemas.ts # shared zod input schemas
blizzard/
tokenManager.ts # OAuth client-credentials + single-flight
client.ts # got wrapper: bearer injection, cache, 401 retry
endpoints/
types.ts # EndpointDef interface, buildPath(), schema helpers
gamedata.ts # 161 Game Data API endpoint definitions
profileEndpoints.ts # 35 Profile API endpoint definitions
schemas/
characterSchemas.ts # zod response schemas
achievementSchemas.ts
dto/
characterDto.ts # normalized character DTO
timeline.ts # achievement timeline builder
util/
http.ts # got defaults
cache.ts # TTL cache
logger.ts # pino (stderr)
test/
auth.test.ts # OAuth2 auth integration testsEndpoints are defined declaratively in gamedata.ts and profileEndpoints.ts. Each entry specifies a tool name, path template, namespace type, and zod input schema. The tools.ts module iterates over the registry and auto-registers every entry as an MCP tool, injecting region and locale parameters automatically.
This server cannot be installed
Resources
Unclaimed servers have limited discoverability.
Looking for Admin?
If you are the server author, to access and configure the admin panel.
Latest Blog Posts
MCP directory API
We provide all the information about MCP servers via our MCP API.
curl -X GET 'https://glama.ai/api/mcp/v1/servers/brunofin/wow-mcp'
If you have feedback or need assistance with the MCP directory API, please join our Discord server