mcp-server-wazuh
Supports configuration through environment variables stored in a .env file for local development, allowing easy setup of Wazuh API connection details
Click on "Install Server".
Wait a few minutes for the server to deploy. Once ready, it will show a "Started" state.
In the chat, type
@followed by the MCP server name and your instructions, e.g., "@mcp-server-wazuhshow me critical vulnerabilities on our web servers"
That's it! The server will respond to your query, and you can continue using it as needed.
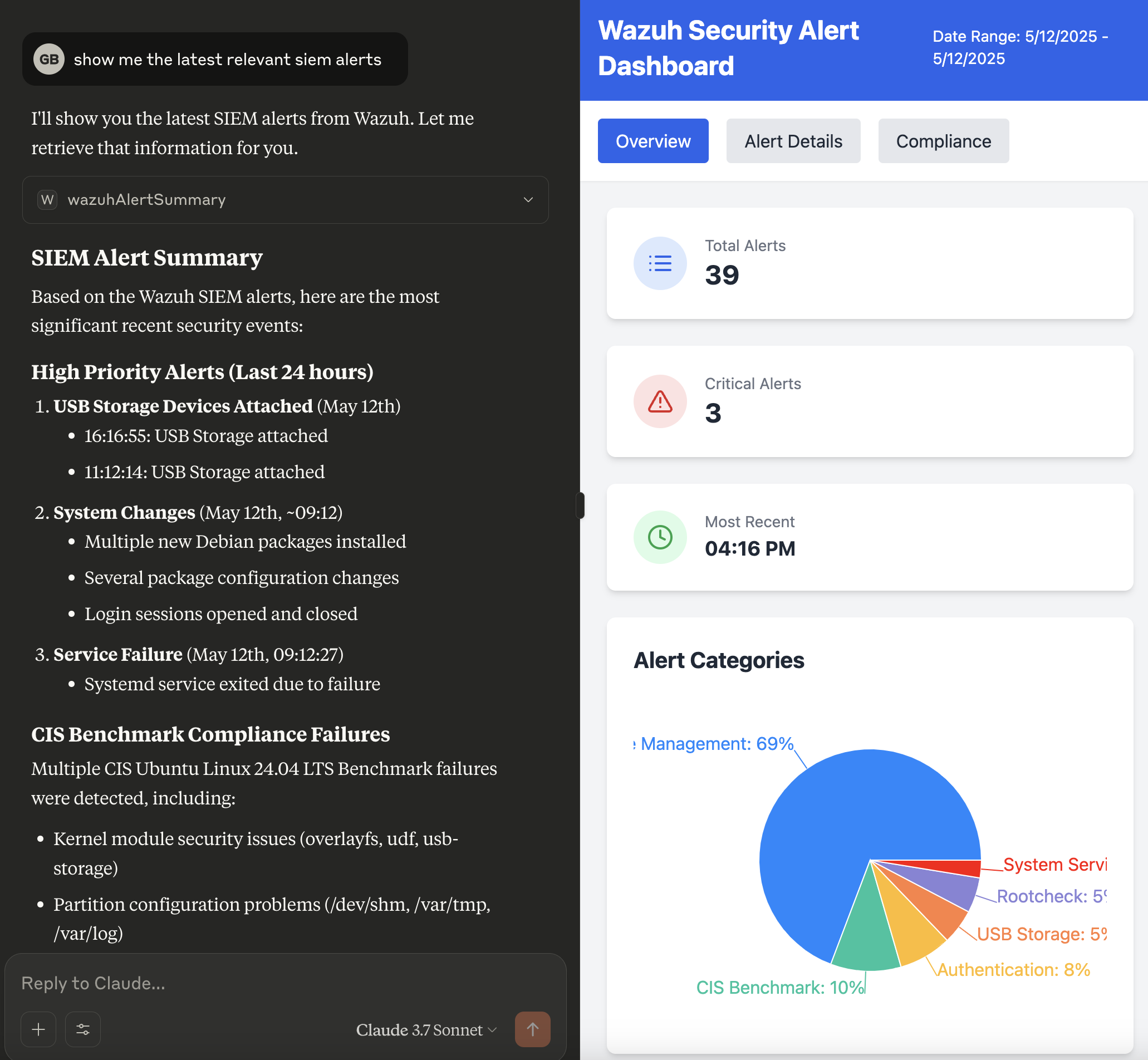
Here is a step-by-step guide with screenshots.
Wazuh MCP Server - Talk to your SIEM
A Rust-based server designed to bridge the gap between a Wazuh Security Information and Event Management (SIEM) system and applications requiring contextual security data, specifically tailored for the Claude Desktop Integration using the Model Context Protocol (MCP).
Overview
Modern AI assistants like Claude can benefit significantly from real-time context about the user's security environment. The Wazuh MCP Server bridges this gap by providing comprehensive access to Wazuh SIEM data through natural language interactions.
This server transforms complex Wazuh API responses into MCP-compatible format, enabling AI assistants to access:
Security Alerts & Events from the Wazuh Indexer for threat detection and incident response
Agent Management & Monitoring including health status, system processes, and network ports
Vulnerability Assessment data for risk management and patch prioritization
Security Rules & Configuration for detection optimization and compliance validation
System Statistics & Performance metrics for operational monitoring and audit trails
Log Analysis & Forensics capabilities for incident investigation and compliance reporting
Cluster Health & Management for infrastructure reliability and availability requirements
Compliance Monitoring & Gap Analysis for regulatory frameworks like PCI-DSS, HIPAA, SOX, and GDPR
Rather than requiring manual API calls or complex queries, security teams can now ask natural language questions like "Show me critical vulnerabilities on web servers," "What processes are running on agent 001?" or "Are we meeting PCI-DSS logging requirements?" and receive structured, actionable data from their Wazuh deployment.
This approach is particularly valuable for compliance teams who need to quickly assess security posture, identify gaps in monitoring coverage, validate rule effectiveness, and generate evidence for audit requirements across distributed infrastructure.
Related MCP server: mcp-server-pacman
Example Use Cases
The Wazuh MCP Server provides direct access to Wazuh security data through natural language interactions, enabling several practical use cases:
Security Alert Analysis
Alert Triage and Investigation: Query recent security alerts with
get_wazuh_alert_summaryto quickly identify and prioritize threats requiring immediate attention.Alert Pattern Recognition: Analyze alert trends and patterns to identify recurring security issues or potential attack campaigns.
Vulnerability Management
Agent Vulnerability Assessment: Use
get_wazuh_vulnerability_summaryandget_wazuh_critical_vulnerabilitiesto assess security posture of specific agents and prioritize patching efforts.Risk-Based Vulnerability Prioritization: Correlate vulnerability data with agent criticality and exposure to focus remediation efforts.
System Monitoring and Forensics
Process Analysis: Investigate running processes on agents using
get_wazuh_agent_processesfor threat hunting and system analysis.Network Security Assessment: Monitor open ports and network services with
get_wazuh_agent_portsto identify potential attack vectors.Agent Health Monitoring: Track agent status and connectivity using
get_wazuh_running_agentsto ensure comprehensive security coverage.
Security Operations Intelligence
Rule Effectiveness Analysis: Review and analyze security detection rules with
get_wazuh_rules_summaryto optimize detection capabilities.Manager Performance Monitoring: Track system performance and statistics using tools like
get_wazuh_weekly_stats,get_wazuh_remoted_stats, andget_wazuh_log_collector_stats.Cluster Health Management: Monitor Wazuh cluster status with
get_wazuh_cluster_healthandget_wazuh_cluster_nodesfor operational reliability.
Incident Response and Forensics
Log Analysis: Search and analyze manager logs using
search_wazuh_manager_logsandget_wazuh_manager_error_logsfor incident investigation.Agent-Specific Investigation: Combine multiple tools to build comprehensive profiles of specific agents during security incidents.
Natural Language Security Queries: Ask complex security questions in natural language and receive structured data from multiple Wazuh components.
Operational Efficiency
Automated Reporting: Generate security reports and summaries through conversational interfaces without manual API calls.
Cross-Component Analysis: Correlate data from both Wazuh Indexer (alerts) and Wazuh Manager (agents, rules, vulnerabilities) for comprehensive security insights.
Multilingual Security Operations: Access Wazuh data and receive insights in multiple languages for global security teams.
Threat Intelligence Gathering and Response
For enhanced threat intelligence and incident response capabilities, the Wazuh MCP Server can be combined with complementary security MCP servers:
Server | Description |
Artifact analysis and IOC enrichment via 140+ analyzers | |
Case management and incident response orchestration | |
Threat intelligence sharing and IOC lookup |
Enhanced Capabilities with Cortex Integration:
Artifact Analysis: Automatically analyze suspicious files, URLs, domains, and IP addresses found in Wazuh alerts using Cortex's 140+ analyzers
IOC Enrichment: Enrich indicators of compromise (IOCs) from Wazuh alerts with threat intelligence from multiple sources including VirusTotal, Shodan, MISP, and more
Automated Threat Hunting: Combine Wazuh's detection capabilities with Cortex's analysis engines to automatically investigate and classify threats
Multi-Source Intelligence: Leverage analyzers for reputation checks, malware analysis, domain analysis, and behavioral analysis
Response Orchestration: Use analysis results to inform automated response actions and alert prioritization
Enhanced Capabilities with TheHive Integration:
Case Creation: Automatically create cases in TheHive from Wazuh alerts for structured incident tracking
Alert Correlation: Link related Wazuh alerts to existing cases for comprehensive incident timelines
Task Management: Create and track investigation tasks based on alert severity and type
Observable Management: Extract and manage IOCs as observables within case investigations
Collaboration: Enable security team collaboration on incidents detected by Wazuh
Enhanced Capabilities with MISP Integration:
IOC Lookup: Check if indicators from Wazuh alerts are known in your threat intelligence database
Threat Context: Retrieve event context, threat actor attribution, and MITRE ATT&CK mappings for IOCs
False Positive Reduction: Validate IOCs against MISP warninglists to reduce false positives
Sighting Tracking: Record and query sighting history to assess IOC prevalence
Galaxy Exploration: Access threat actor profiles, malware families, and attack patterns
Example Workflow:
Wazuh detects a suspicious file hash or network connection in an alert
The AI assistant queries the MISP MCP Server to check if the IOC is known in threat intelligence
If unknown, the Cortex MCP Server analyzes the artifact using multiple analyzers
Results from VirusTotal, hybrid analysis, domain reputation, and other sources are correlated
A case is created in TheHive via the TheHive MCP Server to track the investigation
The combined intelligence provides context for incident response decisions
Findings can be used to update Wazuh rules or trigger additional monitoring
Requirements
An MCP (Model Context Protocol) compatible LLM client (e.g., Claude Desktop)
A running Wazuh server (v4.12 recommended) with the API enabled and accessible.
Network connectivity between this server and the Wazuh API (if API interaction is used).
Installation
Option 1: Download Pre-built Binary (Recommended)
Download the Binary:
Go to the Releases page of the
mcp-server-wazuhGitHub repository.Download the appropriate binary for your operating system (e.g.,
mcp-server-wazuh-linux-amd64,mcp-server-wazuh-macos-amd64,mcp-server-wazuh-macos-arm64,mcp-server-wazuh-windows-amd64.exe).Make the downloaded binary executable (e.g.,
chmod +x mcp-server-wazuh-linux-amd64).(Optional) Rename it to something simpler like
mcp-server-wazuhand move it to a directory in your system'sPATHfor easier access.
Option 2: Docker
Pull the Docker Image:
docker pull ghcr.io/gbrigandi/mcp-server-wazuh:latest
Option 3: Build from Source
Prerequisites:
Install Rust: https://www.rust-lang.org/tools/install
Build:
git clone https://github.com/gbrigandi/mcp-server-wazuh.git cd mcp-server-wazuh # Build with stdio transport only (default) cargo build --release # Build with HTTP transport support cargo build --release --features httpThe binary will be available at
target/release/mcp-server-wazuh.
Configure Your LLM Client
The method for configuring your LLM client will vary depending on the client itself. For clients that support MCP (Model Context Protocol), you will typically need to point the client to the path of the mcp-server-wazuh executable.
Example for Claude Desktop:
Configure your claude_desktop_config.json file:
{
"mcpServers": {
"wazuh": {
"command": "/path/to/mcp-server-wazuh",
"args": [],
"env": {
"WAZUH_API_HOST": "your_wazuh_manager_api_host",
"WAZUH_API_PORT": "55000",
"WAZUH_API_USERNAME": "your_wazuh_api_user",
"WAZUH_API_PASSWORD": "your_wazuh_api_password",
"WAZUH_INDEXER_HOST": "your_wazuh_indexer_host",
"WAZUH_INDEXER_PORT": "9200",
"WAZUH_INDEXER_USERNAME": "your_wazuh_indexer_user",
"WAZUH_INDEXER_PASSWORD": "your_wazuh_indexer_password",
"WAZUH_VERIFY_SSL": "false",
"WAZUH_TEST_PROTOCOL": "https",
"RUST_LOG": "info"
}
}
}
}Replace /path/to/mcp-server-wazuh with the actual path to your binary and configure the environment variables as detailed in the Configuration section.
Once configured, your LLM client should be able to launch and communicate with the mcp-server-wazuh to access Wazuh security data.
If using Docker, create a .env file with your Wazuh configuration:
WAZUH_API_HOST=your_wazuh_manager_api_host
WAZUH_API_PORT=55000
WAZUH_API_USERNAME=your_wazuh_api_user
WAZUH_API_PASSWORD=your_wazuh_api_password
WAZUH_INDEXER_HOST=your_wazuh_indexer_host
WAZUH_INDEXER_PORT=9200
WAZUH_INDEXER_USERNAME=your_wazuh_indexer_user
WAZUH_INDEXER_PASSWORD=your_wazuh_indexer_password
WAZUH_VERIFY_SSL=false
WAZUH_TEST_PROTOCOL=https
RUST_LOG=infoConfigure your claude_desktop_config.json file:
{
"mcpServers": {
"wazuh": {
"command": "docker",
"args": [
"run", "--rm", "-i",
"--env-file", "/path/to/your/.env",
"ghcr.io/gbrigandi/mcp-server-wazuh:latest"
]
}
}
}Configuration
Configuration is managed through environment variables. A .env file can be placed in the project root for local development.
Variable | Description | Default | Required |
| Hostname or IP address of the Wazuh Manager API server. |
| Yes |
| Port number for the Wazuh Manager API. |
| Yes |
| Username for Wazuh Manager API authentication. |
| Yes |
| Password for Wazuh Manager API authentication. |
| Yes |
| Hostname or IP address of the Wazuh Indexer API server. |
| Yes |
| Port number for the Wazuh Indexer API. |
| Yes |
| Username for Wazuh Indexer API authentication. |
| Yes |
| Password for Wazuh Indexer API authentication. |
| Yes |
| Set to |
| No |
| Protocol for Wazuh connections (e.g., "http", "https"). Overrides client default. |
| No |
| Log level (e.g., |
| No |
Note on WAZUH_VERIFY_SSL: For production environments, it is strongly recommended to set WAZUH_VERIFY_SSL=true and ensure proper certificate validation for both Wazuh Manager API and Wazuh Indexer connections. Setting it to false disables certificate checks, which is insecure.
The "Required: Yes" indicates that these variables are essential for the server to connect to the respective Wazuh components. While defaults are provided, they are unlikely to match a production or non-local setup.
Building
Prerequisites
Install Rust: https://www.rust-lang.org/tools/install
Install Docker and Docker Compose (optional, for containerized deployment): https://docs.docker.com/get-docker/
Local Development
Clone the repository:
git clone https://github.com/gbrigandi/mcp-server-wazuh.git cd mcp-server-wazuhConfigure (if using Wazuh API):
Copy the example environment file:
cp .env.example .envEdit the
.envfile with your specific Wazuh API details (e.g.WAZUH_API_HOST,WAZUH_API_PORT).
Build:
# Build with default features (stdio transport only) cargo build # Build with HTTP transport support cargo build --features httpRun:
# Run with stdio transport (default) cargo run # Run with HTTP transport (requires --features http during build) cargo run --features http -- --transport http # Or use the run script (which might set up stdio mode): # ./run.sh
Transport Modes
The Wazuh MCP Server supports two transport modes for communication with MCP clients:
stdio Transport (Default)
The stdio transport is the default mode, ideal for local integrations where the MCP client launches the server as a child process. Communication occurs via stdin/stdout using JSON-RPC 2.0 messages.
# Run with stdio transport (default)
mcp-server-wazuh
# Explicit stdio transport
mcp-server-wazuh --transport stdioStreamable HTTP Transport
The HTTP transport enables remote server deployment, allowing MCP clients to connect over the network. This mode implements the MCP Streamable HTTP specification with Server-Sent Events (SSE) support.
# Run with HTTP transport on default address (127.0.0.1:8080)
mcp-server-wazuh --transport http
# Run with custom host and port
mcp-server-wazuh --transport http --host 0.0.0.0 --port 3000HTTP Transport Features:
Single
/mcpendpoint for all MCP communicationPOST requests with JSON-RPC messages
Server-Sent Events (SSE) for streaming responses
Session management with
MCP-Session-IdheaderProtocol version:
2025-06-18(MCP spec supported by rmcp 0.10)
Security Note: By default, HTTP transport binds to 127.0.0.1 (localhost only). When binding to 0.0.0.0 for remote access, ensure proper network security measures (firewall rules, reverse proxy with TLS, etc.) are in place.
CLI Arguments
Argument | Description | Default |
| Transport mode: |
|
| HTTP server bind address (only for http transport) |
|
| HTTP server port (only for http transport) |
|
Architecture
The server is built using the rmcp framework (v0.10+) and facilitates communication between MCP clients (e.g., Claude Desktop, IDE extensions) and the Wazuh MCP Server. The server supports both stdio and Streamable HTTP transports and interacts with the Wazuh Indexer and Wazuh Manager APIs to fetch security alerts and other data.
sequenceDiagram
participant ClientApp as Client Application (e.g., IDE Extension / Claude Desktop)
participant WazuhMCPServer as Wazuh MCP Server (this application)
participant WazuhAPI as Wazuh API
ClientApp->>+WazuhMCPServer: (stdio) MCP Initialize
WazuhMCPServer-->>-ClientApp: (stdout) MCP Initialized
ClientApp->>+WazuhMCPServer: (stdio) MCP Request (tools/list)
WazuhMCPServer->>WazuhMCPServer: Parse MCP Request
WazuhMCPServer->>WazuhMCPServer: Process internally
WazuhMCPServer-->>-ClientApp: (stdout) MCP Response (available tools)
ClientApp->>+WazuhMCPServer: (stdio) MCP Request (tools/call for wazuhAlerts)
WazuhMCPServer->>WazuhMCPServer: Parse MCP Request
WazuhMCPServer->>+WazuhAPI: Request Wazuh Alerts (with WAZUH_API_USERNAME, WAZUH_API_PASSWORD)
WazuhAPI-->>-WazuhMCPServer: Wazuh Alert Data (JSON)
WazuhMCPServer->>WazuhMCPServer: Transform Wazuh Alerts to MCP Format
WazuhMCPServer-->>-ClientApp: (stdout) MCP Response (alerts)Data Flow (stdio focus):
An application (e.g., an IDE extension, a CLI tool) launches the Wazuh MCP Server as a child process.
The application sends MCP-formatted requests (commands) to the server's
stdin.The Wazuh MCP Server reads the command from
stdin.Processing:
The server parses the MCP command.
If the command requires fetching data from Wazuh (e.g., "get latest alerts"):
The server connects to the Wazuh API (authenticating if necessary using configured credentials like
WAZUH_API_USERNAME,WAZUH_API_PASSWORD).It fetches the required data (e.g., security alerts).
The server's transformation logic processes each alert, mapping Wazuh fields to MCP format.
If the command is internal (e.g., a status check specific to the MCP server), it processes it directly.
The server sends an MCP-formatted JSON response (e.g., transformed alerts, command acknowledgment, or error messages) to the application via its
stdout.The application reads and processes the MCP response from the server's
stdout.
This stdio interaction allows for tight integration with local development tools or other applications that can manage child processes. An optional HTTP endpoint (/mcp) may also be available for clients that prefer polling.
The server communicates via stdin and stdout using JSON-RPC 2.0 messages, adhering to the Model Context Protocol (MCP).
Example interaction flow:
Client Application (e.g., IDE extension) starts the
mcp-server-wazuhprocess.Client sends
initializerequest to server'sstdin:{ "jsonrpc": "2.0", "id": 0, "method": "initialize", "params": { "protocolVersion": "2025-06-18", "capabilities": { "sampling": {}, "roots": { "listChanged": true } }, "clientInfo": { "name": "mcp-inspector", "version": "0.11.0" } } }Server sends
initializeresponse to client viastdout:{ "jsonrpc": "2.0", "id": 1, "result": { "protocolVersion": "2025-06-18", "capabilities": { "prompts": {}, "resources": {}, "tools": {} }, "serverInfo": { "name": "mcp-server-wazuh", "version": "0.3.0" }, "instructions": "This server provides tools to interact with a Wazuh SIEM instance for security monitoring and analysis.\nAvailable tools:\n- 'get_wazuh_alert_summary': Retrieves a summary of Wazuh security alerts. Optionally takes 'limit' parameter to control the number of alerts returned (defaults to 100)." } }Client sends
notifications/initializedto server'sstdin: (This is a notification, soidis omitted by the client.){ "jsonrpc": "2.0", "method": "notifications/initialized" }Client requests available tools by sending
tools/listto server'sstdin:{ "jsonrpc": "2.0", "id": 1, "method": "tools/list", "params": {} }Server responds with the list of tools to client via
stdout:{ "jsonrpc": "2.0", "id": 2, "result": { "tools": [ { "name": "get_wazuh_alert_summary", "description": "Retrieves a summary of Wazuh security alerts. Returns formatted alert information including ID, timestamp, and description.", "inputSchema": { "$schema": "http://json-schema.org/draft-07/schema#", "properties": { "limit": { "description": "Maximum number of alerts to retrieve (default: 100)", "format": "uint32", "minimum": 0.0, "type": ["integer", "null"] } }, "title": "GetAlertSummaryParams", "type": "object" } } ] } }Client calls the
get_wazuh_alert_summarytool by sendingtools/callto server'sstdin:{ "jsonrpc": "2.0", "id": 3, "method": "tools/call", "params": { "name": "get_wazuh_alert_summary", "arguments": { "limit": 5 } } }Server receives on
stdin, processes theget_wazuh_alert_summarycall (which involves querying the Wazuh Indexer API and transforming the data).Server sends
tools/callresponse with formatted alerts to client viastdout:{ "jsonrpc": "2.0", "id": 3, "result": { "content": [ { "type": "text", "text": "Alert ID: 1747091815.1212763\nTime: 2024-01-15T10:30:45.123Z\nAgent: web-server-01\nLevel: 7\nDescription: Attached USB Storage" }, { "type": "text", "text": "Alert ID: 1747066333.1207112\nTime: 2024-01-15T10:25:12.456Z\nAgent: database-server\nLevel: 5\nDescription: New dpkg (Debian Package) installed." } ], "isError": false } }Or, if no alerts are found:
{ "jsonrpc": "2.0", "id": 3, "result": { "content": [ { "type": "text", "text": "No Wazuh alerts found." } ], "isError": false } }Or, if there's an error connecting to Wazuh:
{ "jsonrpc": "2.0", "id": 3, "result": { "content": [ { "type": "text", "text": "Error retrieving alerts from Wazuh: HTTP request error: connection refused" } ], "isError": true } }
Development & Testing
Code Style: Uses standard Rust formatting (
cargo fmt).Linting: Uses Clippy (
cargo clippy).Testing: Contains unit tests for transformation logic and integration tests. For stdio, tests might involve piping input/output to a test harness. For HTTP, tests use a mock Wazuh API server (
httpmock) and a test MCP client.# Run all tests cargo test # Run specific integration test (example for HTTP tests) # cargo test --test integration_test # Run tests with detailed logging RUST_LOG=debug cargo testSee
tests/README.mdfor more details on running tests and using the test client CLI.
License
This project is licensed under the MIT License.
This server cannot be installed
Maintenance
Appeared in Searches
Latest Blog Posts
MCP directory API
We provide all the information about MCP servers via our MCP API.
curl -X GET 'https://glama.ai/api/mcp/v1/servers/gbrigandi/mcp-server-wazuh'
If you have feedback or need assistance with the MCP directory API, please join our Discord server