osv-ui-mcp
The osv-ui-mcp server enables AI agents to scan projects for CVE vulnerabilities, visualize findings, and apply fixes with a human-in-the-loop workflow. All analysis runs 100% locally, ensuring your code never leaves your environment.
Scan projects for CVEs (
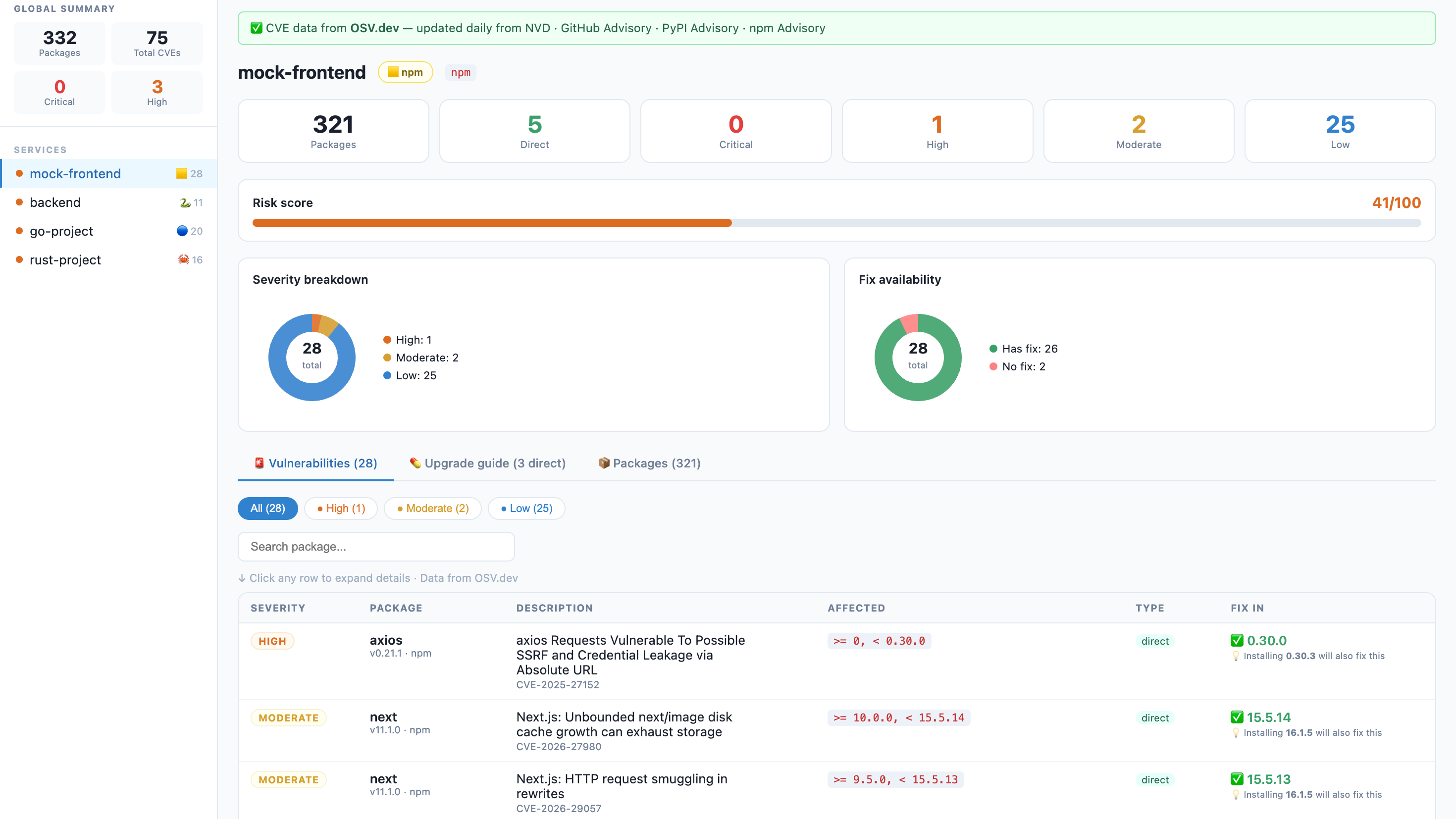
scan_project): Automatically detect and scan manifest files (e.g.,package-lock.json,requirements.txt,go.sum,Cargo.lock,pom.xml) across npm, Python, Go, Rust, Java, PHP, and Ruby ecosystems. Queries live CVE data from OSV.dev and returns structured reports with severity counts, risk scores, and fix recommendations. Supports filtering by severity (critical, high, moderate, low).Launch a visual dashboard (
open_dashboard): Opens a zero-config, privacy-first browser-based dashboard for human review of CVE details, severity charts, and upgrade guides — the recommended step before applying any fixes.Preview fix commands (
get_fix_commands): Retrieves safe upgrade commands (e.g.,npm install,pip install) for vulnerable packages without executing them, allowing users to review proposed changes before action.Apply security fixes (
apply_fixes): Executes package upgrade commands to remediate CVEs. Supports dry-run mode for final confirmation; requires explicit package selection to prevent unintended modifications.
Utilizes the GitHub Advisory Database as a core source for vulnerability data to provide accurate security assessments.
Enables security auditing within GitLab CI/CD pipelines to monitor for vulnerabilities and block deployments containing critical security risks.
Scans npm projects by parsing package-lock.json files to identify security vulnerabilities, calculate risk scores, and provide clear upgrade guides.
Provides specific support for auditing Python dependencies defined in poetry.lock manifest files.
Integrates with the PyPI Advisory Database to identify known vulnerabilities in Python package dependencies.
Audits Python projects for CVEs by scanning manifest files such as requirements.txt, Pipfile.lock, and poetry.lock.
Identifies and reports known security vulnerabilities in Rust projects by analyzing Cargo.lock files.
osv-ui
A beautiful, zero-config visual CVE dashboard for npm, Python, Go, Rust, Java, PHP, and Ruby projects.
One command. No signup. No API key. Runs 100% locally — your code never leaves your machine.
🇻🇳 Tiếng Việt · 🇺🇸 English · 🇨🇳 中文 · 🇯🇵 日本語
The problem
$ npm audit
# ... 300 lines of this ...
# moderate Regular Expression Denial of Service in semver
# package semver
# patched in >=7.5.2
# ...
# 12 vulnerabilities (3 moderate, 6 high, 3 critical)Nobody reads that. Security gets ignored. Dependencies stay vulnerable.
The solution
npx osv-ui→ Opens a dashboard. Every CVE, every fix, all your services. Done.
Why give it a try?
Zero-config: No complex setup, no signup, no API key required.
Privacy First: Analysis is done 100% on your machine.
Fast & Visual: Real-time Risk Scores, vulnerability charts, and clear upgrade guides in seconds.
Multi-platform: Native support for Node.js (npm), Python, Go, Rust, Java, PHP, and Ruby.
Features
🌐 Multi-Ecosystem | Scans |
📡 Live CVE data | Powered by OSV.dev — updated daily from NVD, GitHub Advisory, PyPI Advisory. No API key. |
🏢 Multi-service | Scan your entire monorepo in one command — frontend, backend, workers, ML services |
💊 Fix guide | Dependabot-style upgrade table: current version → safe version + one-click copy command |
🔌 Built-in REST API | Power your own security dashboards with |
🎯 Risk score | 0–100 per service so you know where to focus first |
🔍 CVE drill-down | Click any row — CVSS score, description, NVD link, GitHub Advisory link |
🌙 Dark Mode | Eye-friendly security audits, day or night |
Quick start
Scan current directory:
npx osv-uiScan a monorepo (multiple services at once):
npx osv-ui ./frontend ./api ./worker ./ml-serviceAuto-discover all services under the current directory:
npx osv-ui -dAdd to your package.json scripts:
{
"scripts": {
"audit:ui": "npx osv-ui",
"audit:all": "npx osv-ui ./frontend ./api ./worker"
}
}--discover, -d Auto-find service dirs that contain a supported manifest
--port=2003 Use a custom port (default: 2003)
--json[=file] Save report as JSON without opening browser (defaults to osv-report.json)
--html[=file] Save report as HTML without opening browser (defaults to osv-report.html)
--no-open Don't auto-open the browser
--offline Skip OSV.dev lookup — parse manifests only
-h, --help Show help message🤖 AI Agent Integration (MCP)
osv-ui is now a Model Context Protocol (MCP) server. This allows AI agents like Claude Desktop, Cursor, and Claude Code to:
Scan your project for CVEs automatically.
Open the visual dashboard for you to review findings (Human-in-the-loop).
Apply fixes after your explicit confirmation.
Quick setup (npx):
{
"mcpServers": {
"osv-ui": {
"command": "npx",
"args": ["-y", "osv-ui-mcp"]
}
}
}See the MCP Package README for detailed setup instructions.
🔌 Powerful built-in API
osv-ui isn't just a dashboard; it's a security data engine.
Once the dashboard is running, you can pull the raw security data for your whole project:
# Get full JSON payload for all services
curl http://localhost:2003/api/data
# Use it in your custom scripts
curl -s http://localhost:2003/api/data | jq '.[0].vulns'Supported manifest files
Ecosystem | Files |
npm / JS |
|
Python |
|
Go |
|
Rust |
|
Java |
|
PHP |
|
Ruby |
|
More ecosystems coming — see Roadmap.
How it works
Your project files
│
├─ package-lock.json ──┐
├─ Pipfile / poetry ──┤──► parser ──► package list
├─ go.sum / Cargo.lock ──┘
│
▼
OSV.dev batch API (free, no key)
│
▼
CVE matches + fix versions
│
▼
Express server → browser dashboard
http://localhost:2003CVE data comes from OSV.dev — a free, open database maintained by Google that aggregates:
🇺🇸 NVD — NIST National Vulnerability Database
🐙 GitHub Advisory Database (GHSA)
📦 npm Advisory Database
🦀 RustSec · Go Vuln DB · OSS-Fuzz · and more
Updated daily. No account. No rate limit. No vendor lock-in.
Works great alongside osv-scanner (Google)
osv-ui and osv-scanner use the same OSV.dev data source. osv-ui adds the visual layer that osv-scanner lacks:
Browser dashboard instead of terminal output
Multi-service sidebar
Dependabot-style upgrade guide with copy commands
vs alternatives
osv-ui |
| Snyk | Dependabot | |
Visual dashboard | ✅ | ❌ terminal only | ✅ | ✅ |
npm support | ✅ | ✅ | ✅ | ✅ |
Python support | ✅ | ❌ | ✅ | ✅ |
Multi-service in one view | ✅ | ❌ | ✅ paid | ✅ |
No signup required | ✅ | ✅ | ❌ | ❌ |
Works on GitLab Free | ✅ | ✅ | ❌ | ❌ |
Self-hosted / local | ✅ | ✅ | ❌ | ❌ |
Fix commands | ✅ | partial | ✅ | ✅ |
Open source | ✅ | ✅ | ❌ | ❌ |
GitLab CI — block deploys on critical CVEs
No Dependabot on GitLab Free? Add this to .gitlab-ci.yml:
audit:
stage: test
image: node:20-alpine
script:
- npm audit --json > /tmp/audit.json || true
- |
node -e "
const r = require('/tmp/audit.json');
const crit = Object.values(r.vulnerabilities || {})
.filter(v => v.severity === 'critical').length;
if (crit > 0) {
console.error('BLOCKED: ' + crit + ' critical CVE(s). Run: npx osv-ui');
process.exit(1);
}
console.log('OK: no critical vulnerabilities');
"
artifacts:
paths: [/tmp/audit.json]
when: alwaysRequirements
Node.js >= 16
Internet access for OSV.dev queries — or use
--offlinenpm projects: run
npm installfirst sopackage-lock.jsonexistsPython projects: any of the supported manifest files listed above
Roadmap
All contributions are welcome. If you want to work on something, open an issue first so we can coordinate.
Go support — parse
go.sum/go.modRust support — parse
Cargo.lockJava / Maven — parse
pom.xmlPHP / Composer — parse
composer.lockRuby / Bundler — parse
Gemfile.lockExport report — save as HTML / JSON
Dark mode — eye-friendly dashboard UI
GitHub Actions — post a CVE diff comment on PRs
SBOM export — CycloneDX / SPDX format
Watch mode — re-scan on manifest file changes
Slack / webhook — notify on new critical CVEs
Contributing
This project is built by the community. All skill levels welcome.
Good first issues:
Add Java/Maven parser (
pom.xml) — follow the pattern insrc/parsers.jsWrite unit tests for the parsers
Improve Python parser edge cases
# Clone and run locally
git clone https://github.com/toan203/osv-ui
cd osv-ui
npm install
# Run against your own project
node bin/cli.js /path/to/your/project
# Run against multiple services
node bin/cli.js ./frontend ./backendPlease read CONTRIBUTING.md for code style and PR process.
License
MIT — use it, fork it, embed it, build on it. Attribution appreciated but not required.
Did osv-ui catch a real CVE in your project?
A ⭐ helps other developers find this tool.
Latest Blog Posts
MCP directory API
We provide all the information about MCP servers via our MCP API.
curl -X GET 'https://glama.ai/api/mcp/v1/servers/toan203/osv-ui'
If you have feedback or need assistance with the MCP directory API, please join our Discord server