Suricata MCP
Click on "Install Server".
Wait a few minutes for the server to deploy. Once ready, it will show a "Started" state.
In the chat, type
@followed by the MCP server name and your instructions, e.g., "@Suricata MCPtest this rule against /tmp/capture.pcap and check if sid 100001 matches"
That's it! The server will respond to your query, and you can continue using it as needed.
Here is a step-by-step guide with screenshots.
Suricata MCP
MCP service for validating Suricata rules against pcap files.
Installation
# 安装依赖
source /path/to/venv/bin/activate
pip install -e .Usage
运行 MCP Server
suricata-mcp或在 Claude Desktop 配置中添加:
{
"mcpServers": {
"suricata": {
"command": "python",
"args": ["-m", "suricata_mcp.server"],
"env": {
"SURICATA_PATH": "/usr/local/bin/suricata"
}
}
}
}Tools
validate_suricata_rule
验证 Suricata 规则语法是否正确。
参数:
rule_content(string, 必需): Suricata 规则内容
validate_suricata_rule_file
验证 Suricata 规则文件语法是否正确。
参数:
rule_path(string, 必需): 规则文件路径
示例:
{
"rule_path": "/path/to/rules.rules"
}test_suricata_rule
测试 Suricata 规则对 pcap 文件是否生效,验证规则是否能匹配到预期告警。
参数:
rule_content(string, 必需): Suricata 规则内容pcap_path(string, 必需): pcap 文件路径expected_sid(integer, 可选): 预期匹配的 signature ID,不提供则从规则中提取
test_suricata_rule_file
测试 Suricata 规则文件对 pcap 文件是否生效。
参数:
rule_path(string, 必需): 规则文件路径pcap_path(string, 必需): pcap 文件路径expected_sids(array of integers, 可选): 预期匹配的 signature IDs
工作流程
规则语法验证: 使用
suricata -S <rule_path> -T验证规则语法pcap 测试: 使用
suricata -r <pcap_path> -S <rule_path> -l <log_path>运行测试告警解析: 解析
eve.json中event_type为alert的记录sid 匹配: 验证规则的 sid 与告警日志中的
signature_id是否一致
自动编写规则
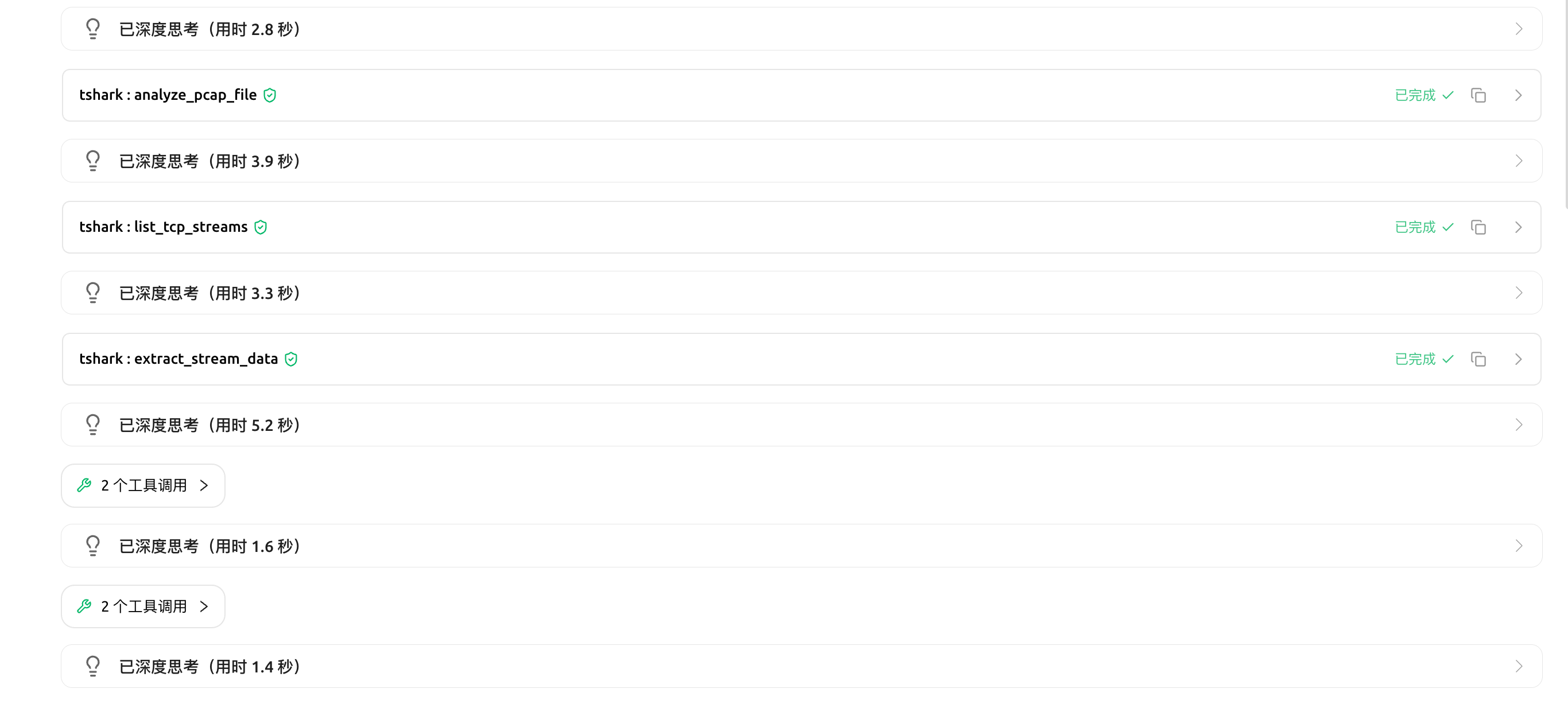
配合: https://github.com/fairyming/tshark_mcp, 可以实现自动分析,编写规则并验证


This server cannot be installed
Resources
Unclaimed servers have limited discoverability.
Looking for Admin?
If you are the server author, to access and configure the admin panel.
Latest Blog Posts
MCP directory API
We provide all the information about MCP servers via our MCP API.
curl -X GET 'https://glama.ai/api/mcp/v1/servers/fairyming/suricata_mcp'
If you have feedback or need assistance with the MCP directory API, please join our Discord server