agent-droid-bridge
Agent Droid Bridge is a FastMCP server that gives AI agents programmatic control over Android devices and emulators via ADB. It exposes the following capabilities:
Screen Interaction: Tap and swipe at pixel coordinates, type text into focused input fields, and send key events (Back, Home, Enter, Delete, etc.)
UI Inspection: Capture screenshots as base64 PNG images or retrieve the full XML UI hierarchy to locate elements, read text, and find resource IDs
Efficient UI Monitoring: Take lightweight UI snapshots and poll for screen changes using a snapshot token, avoiding unnecessary full hierarchy transfers
App & Device Control: Launch apps by
package/activitycomponent name and list all connected devices with their serial numbers, state, and model namesArbitrary ADB Commands: Execute any ADB or ADB shell command, safely parsed via
shlexto prevent shell injectionMulti-Device Handling: Auto-detects a single connected device or requires explicit serial specification when multiple devices are present
Provides programmatic control over Android devices and emulators, enabling AI agents to interact with screens via taps and swipes, inspect UI hierarchies, capture screenshots, and execute ADB commands.
Agent Droid Bridge
Agent Droid Bridge is an MCP server that connects AI agents to Android devices and emulators over ADB. It is built for mobile automation, app testing, dynamic analysis, and reverse engineering: exposing the full surface of ADB as structured tools that any MCP-compatible AI client can call directly. If ADB can do it, an agent can do it.
Purpose-built tools return structured, minimal responses. No raw XML dumps, no wasted context — agents stay fast across long sessions.
Demo
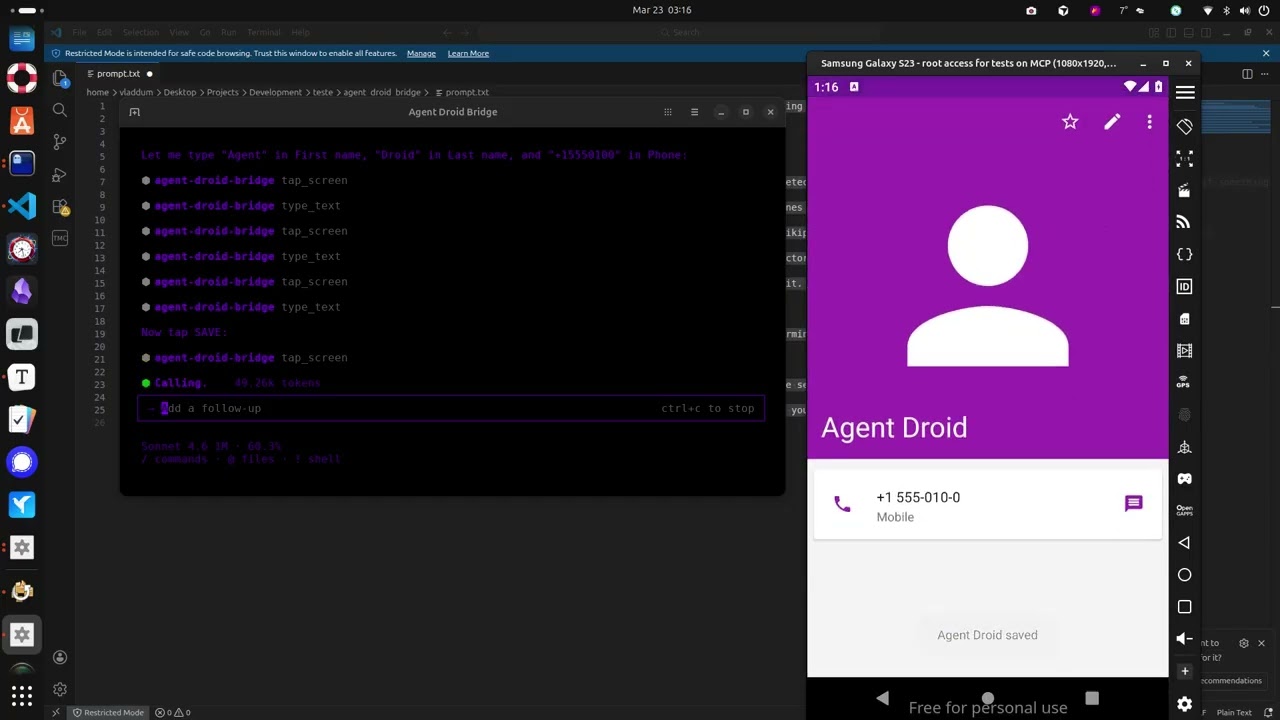
The demo above runs through a few straightforward tasks to show what a connected agent can do, and this is just scratching the surface:
Installs the Paint app, opens it, and draws a house by calculating pixel coordinates for the walls and roof
Opens the device browser, searches for "MCP Wikipedia", navigates to the result page, and takes a screenshot
Opens the Calculator, computes 1337 × 42, and extracts the result to the host machine
Opens Contacts, creates a new entry with a name and phone number, and confirms it saved
Opens the Calendar and schedules an appointment for a specific date
Opens Settings and toggles dark mode
Extracts the Calculator APK from the device to the host machine
Installs Notepad, writes a one-sentence summary of every task completed, and takes a final screenshot
What it does
Tools
14 built-in tools for screen capture, UI inspection, text reading, element extraction, touch and swipe input, text entry, keycode events, app launching, ADB commands, and device inspection
app_managerpack adds 9 tools for package management, app lifecycle, APK extraction, permissions, and intent injection. Load it withADB_EXTRA_TOOL_PACKS=app_managerTool availability is reflected in the server's startup instructions. Agents receive an accurate catalog at connect time
Device handling
Auto-detects a single connected device; prompts for selection when multiple devices are present
Runs over stdio, compatible with any MCP-capable AI client
Structured responses instead of raw XML dumps, keeping agent context lean across long automation runs
Security
Two execution modes:
unrestricted(full ADB access, optional denylist) andrestricted(allowlist-only, blocks everything not explicitly permitted)Set
ADB_ALLOW_SHELL=falseto disable all shell commands regardless of modeHide specific tools from the agent with
ADB_DENIED_TOOLSAll commands parsed via
shlex. No shell injection possible
Observability
Optional session recorder logs every tool call, ADB command, and security event to structured JSONL files. Enable with
MCP_LOG_ENABLED=trueandMCP_LOG_DIR
Use cases
Mobile QA and test automation Automate UI flows across real devices and emulators without modifying the app or writing test code. Tap, swipe, type, read screen content, take screenshots — all from a natural language prompt.
App security research Extract APKs, inspect declared permissions, fire arbitrary intents, and observe runtime behavior on screen. No instrumentation, no jailbreak required.
Dynamic analysis Launch apps in controlled states, drive UI interactions, capture screen state at each step, and pull artifacts — all scriptable through an AI agent.
Development and debugging Install builds, verify UI states, check app info, and run ADB commands without leaving your coding environment.
Install
uvx agent-droid-bridgeNo cloning or virtual environments needed. Requires Python 3.11+ and ADB installed on your host.
uvx is provided by uv. If you don't have it: curl -LsSf https://astral.sh/uv/install.sh | sh
To install from source instead, see docs/setup.md — Option B.
To verify the install: uvx agent-droid-bridge --help
Quick start
Install ADB — see docs/setup.md for platform-specific instructions
Connect an Android device or start an emulator
Add the server to your MCP client config:
{
"mcpServers": {
"agent-droid-bridge": {
"command": "uvx",
"args": ["agent-droid-bridge"],
"env": {
"ADB_EXECUTION_MODE": "unrestricted",
"ADB_ALLOW_SHELL": "true",
"ADB_PATH": "adb",
"ADB_EXTRA_TOOL_PACKS": "",
"MCP_LOG_ENABLED": "false",
"MCP_LOG_DIR": "~/logs/agent-droid-bridge"
}
}
}
}To enable session logging, set MCP_LOG_ENABLED to "true" and update MCP_LOG_DIR to a writable path on your machine.
Variable | Default | Description |
|
| Security mode. |
|
| Set to |
|
| Path to the ADB binary. Replace with a full path if |
| (empty) | Comma-separated list of extra tool packs to load. Set to |
|
| Set to |
| (none) | Directory where session logs are written. Required when |
Prompt your agent to use the
agent-droid-bridgeMCP tools
Full setup guide and environment variable reference: docs/setup.md
Tools
Tool | What it does |
| Returns the current screen as an XML UI hierarchy |
| Captures the screen as a base64-encoded PNG |
| Sends a tap gesture at pixel coordinates |
| Sends a swipe gesture between two points over a given duration |
| Types text into the focused input field |
| Sends an Android keycode event (Back, Home, Enter, etc.) |
| Launches an app by its |
| Runs an arbitrary ADB or ADB shell command |
| Lists all Android devices currently visible to ADB with their serial, state, and model |
| Takes a lightweight UI snapshot and returns a token for use with |
| Polls for a UI change after an action; accepts a snapshot token as baseline; returns hierarchy only when requested |
| Parses the UI hierarchy and returns structured elements with coordinates and interaction properties; supports |
| Returns all visible text on screen sorted top-to-bottom, as plain text |
| Returns structured device information — identity, security posture, and hardware specs — in a single call; supports |
Extra tool packs
Optional packs extend the core toolset. Enable them by setting ADB_EXTRA_TOOL_PACKS in your MCP client config. See docs/extra-tool-packs.md.
app_manager
Package management, app lifecycle control, APK extraction, permission management, and intent injection.
Tool | What it does |
| Lists installed packages with optional filtering, search, and detail levels |
| Returns full static metadata for a single installed app |
| Installs an APK from a host path onto the device |
| Removes an installed app by package name |
| Extracts the installed APK from the device to the host |
| Grants, revokes, checks, or lists runtime permissions for an app |
| Launches an app by package name, auto-resolving the launcher activity |
| Controls app runtime state — stop, clear data, clear cache, enable, disable |
| Fires an intent at a component via |
Full parameter reference: docs/tools.md
Configuration
Configure the server entirely from your MCP client's env block. No files to edit. The env block in the Quick Start above covers the most common settings. For the full reference including security filtering, tool visibility, and timeouts, see docs/configuration.md.
To use a YAML config file instead, set ADB_CONFIG_SOURCE=yaml. See docs/configuration.md for details.
Session recording is separate. Enable it with MCP_LOG_ENABLED=true and MCP_LOG_DIR. Full reference: docs/logging.md.
Documentation
File | Description |
Prerequisites, installation, and MCP client configuration | |
Full parameter reference for all tools | |
Reference for environment variables and | |
Session recorder — log files, levels, retention, and activation | |
Extra tool packs — enabling packs, the pack contract, and writing your own | |
Common setup issues and ADB problems | |
Common multi-tool workflows with examples | |
Release history and version changes |
Contributing
Contributions are welcome. See CONTRIBUTING.md for guidelines on setup, code standards, and submitting pull requests.
To report a security vulnerability, follow the process in SECURITY.md — do not open a public issue.
Maintenance
Latest Blog Posts
MCP directory API
We provide all the information about MCP servers via our MCP API.
curl -X GET 'https://glama.ai/api/mcp/v1/servers/Neverlow512/agent-droid-bridge'
If you have feedback or need assistance with the MCP directory API, please join our Discord server